[UNDER CONSTRUCTION]
A few years ago the company I work for had been hit a couple of times with the then new class of malware called ransomware. At that time, our anti-virus software wasn’t able to stop ransomware, so I was able to come up with a file monitor application called DocWatch. DocWatch would allow users to monitor several disks: local, removable or network for any type of file changes. If files were added, renamed or deleted, the program would track it. Since ransomware, by nature, has to leave instructions behind, DocWatch was able to detect those filenames and send both visual and email alerts.
Since I’m not a commercial software engineer, only myself and a coworker used DocWatch. We managed to catch some ransomware activity on a couple of occasions. The program helped to lessen the number of files which got encrypted. Thankfully, for server based files, they were restored from earlier backups.
Within a year, our anti-virus vendor and others began to do a good job of tracking malicious file activities and ransomware. So, the usefulness of DocWatch was short-lived.
However, another friend who is an independent IT consultant mentioned how he and his clients could use something like DocWatch. He and a couple of clients had been hit with ransomware in the previous year or two, and it was quite unpleasant to recover from.
So, we did some brainstorming and I started writing what would become Keep Watch, a glorified successor to DocWatch.
Program download is here: Setup-KeepWatch
KeepWatch gives users access to a lot of information. The main window is below.
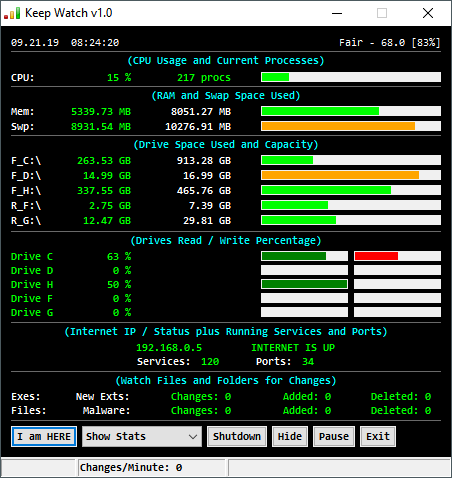
From top to bottom, it shows the following:
- Current Date/Time.
- Current Local Weather. (click it to change the NWS Weather station)
- Relative CPU usage. (click CPU to see processes when CPU usage is >90%)
- Current number of Running Processes. (click procs to view them all)
- Current RAM Memory in use and total RAM.
- Current Swap File Memory in use and total Swap.
- A list of current disk drives [local, removable and network] showing the amount used. (Click any drive to explore it)
- A list of current drives showing relative Read and Write operations.
- The computer’s IP address and Internet status.
- The number of Running Services. (click it to display them)
- The number of active Ports. (click to display them)
- The number of executable file changes since KeepWatch was last started.
- The number of data file changes since KeepWatch was last started.
- The number of malware related file changes since KeepWatch was last started.
- The number of files with categorized Extensions that were created since KeepWatch was last started.
For items 12 to 15, users can click on the White labels to display the actual file changes.
Click on these will display windows like those below. They will display separately unless you choose Realtime display, which displays them together.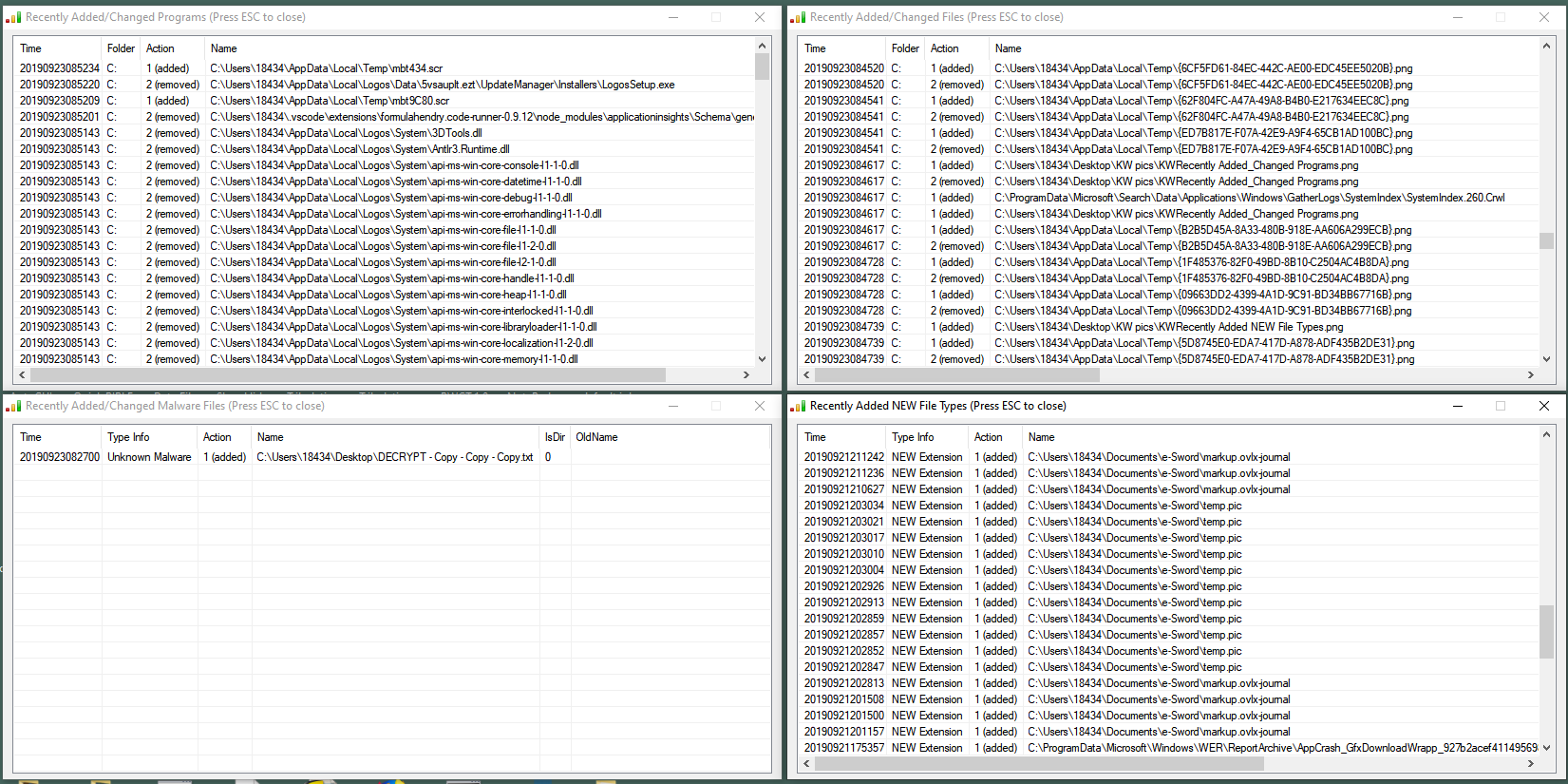 Users can double-click on any file to go to its folder or to add/remove exceptions.
Users can double-click on any file to go to its folder or to add/remove exceptions.
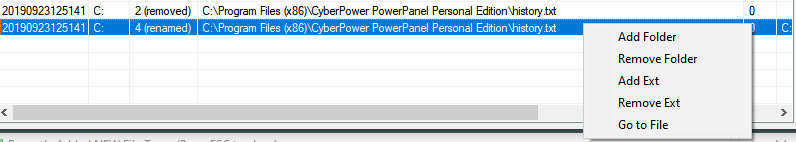 If you want to filter out a folder or add a new file extension as safe, you can double-click a file and choose those options. If the file still exists, you can also Go To its location.
If you want to filter out a folder or add a new file extension as safe, you can double-click a file and choose those options. If the file still exists, you can also Go To its location.
When KeepWatch is started, it will display the local weather if connected. How this looks depends of what Operating System you are using. This is seen with Windows 10. The Weather is checked every 15 minutes and redisplayed only if it has changed. Click the upper right corner weather display to open up a list of NWS weather locations. Find the one closest to you then double click it to select it.

As file changes occur, KeepWatch counters will go up.

If a new file extension is detected, a white on blue popup will appear.
![]()
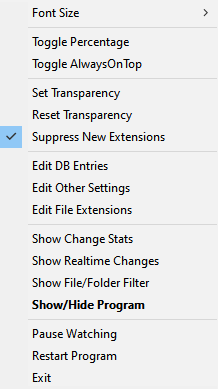
You can add new extensions to the safe list by right-clicking the program’s tray menu icon and choosing Edit File Extensions.
![]()
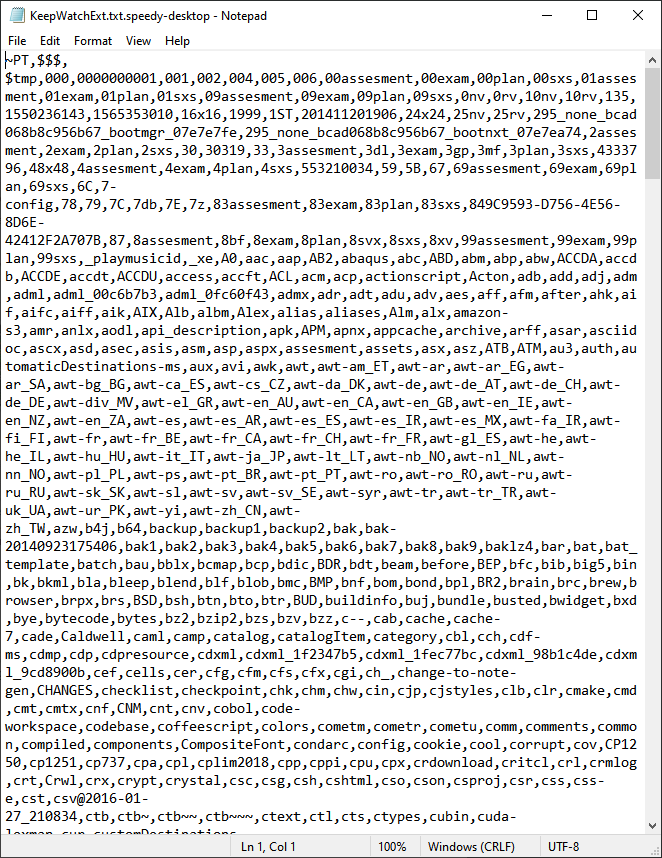
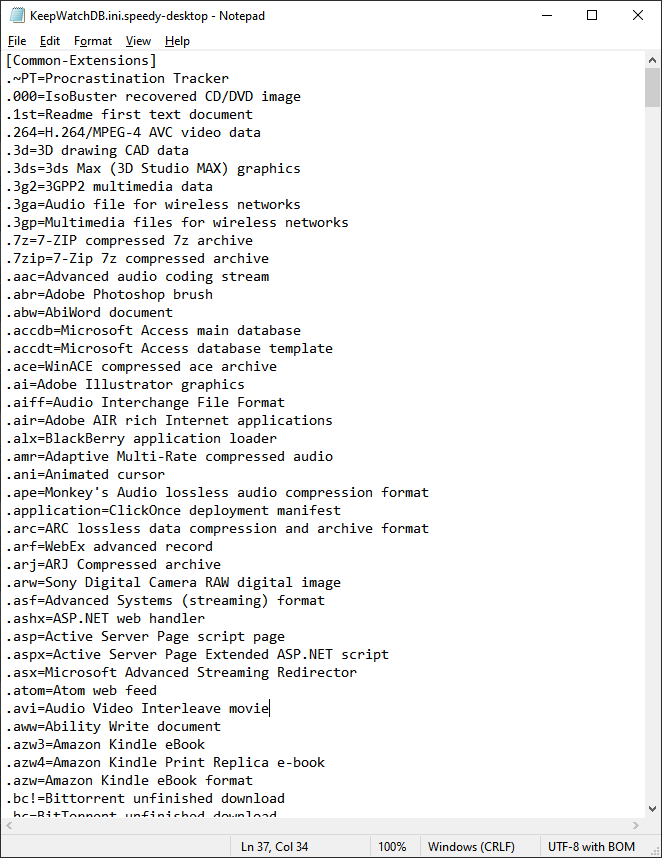
Editing File Extensions will display a lot of short letter sequences separated by commas. When KeepWatch is first run, it scans the user’s hard drive and gathers list of all current extensions. This process will take a few minutes. You may add any new extensions at the top of this list. Just remember to add a comma after it. Most computers will have at least 1,000 different file extensions already.

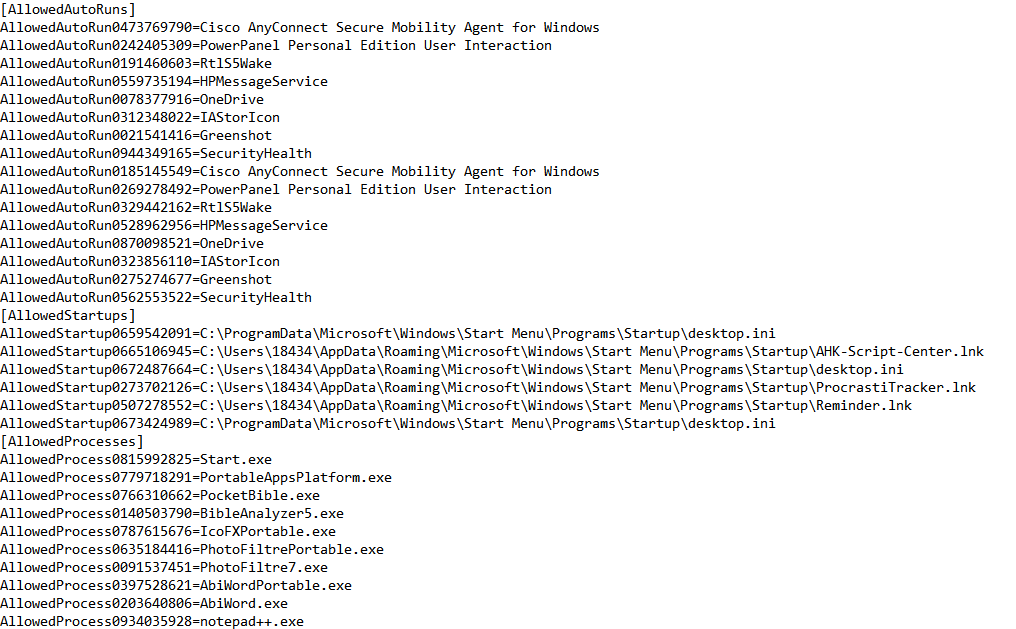
 Keep Watch also gathers the current Startup Items from your computer so it can watch for additions to that list. Additions can potentially be unwanted or malicious software. If it detects a New Process or a New Startup Item, it will allow you to stop or remove it. These lists are kept in the Keep Watch INI file. Weather settings and filtered out folders are also saved here.
Keep Watch also gathers the current Startup Items from your computer so it can watch for additions to that list. Additions can potentially be unwanted or malicious software. If it detects a New Process or a New Startup Item, it will allow you to stop or remove it. These lists are kept in the Keep Watch INI file. Weather settings and filtered out folders are also saved here.

Whenever users view or make changes to these files, the program will ask if you want to Restart.
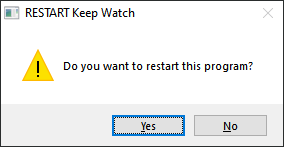
The changes will still be in effect if you don’t Restart. Clicking No will ask if you want to Reset the counters to zero.
Keep Watch will alert users to either detected Malware or if there have been 500 file changes in the last minute, which could be something bad going on. For Malware, the alert appears as below.
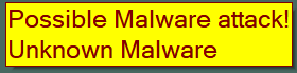
If Keep Watch is hidden, it will redisplay and it’s status bar will turn Red if it suspects a malware attack. The status bar also displays the current changes in the last minute, if any disk is 90% full and other tidbits.
![]()
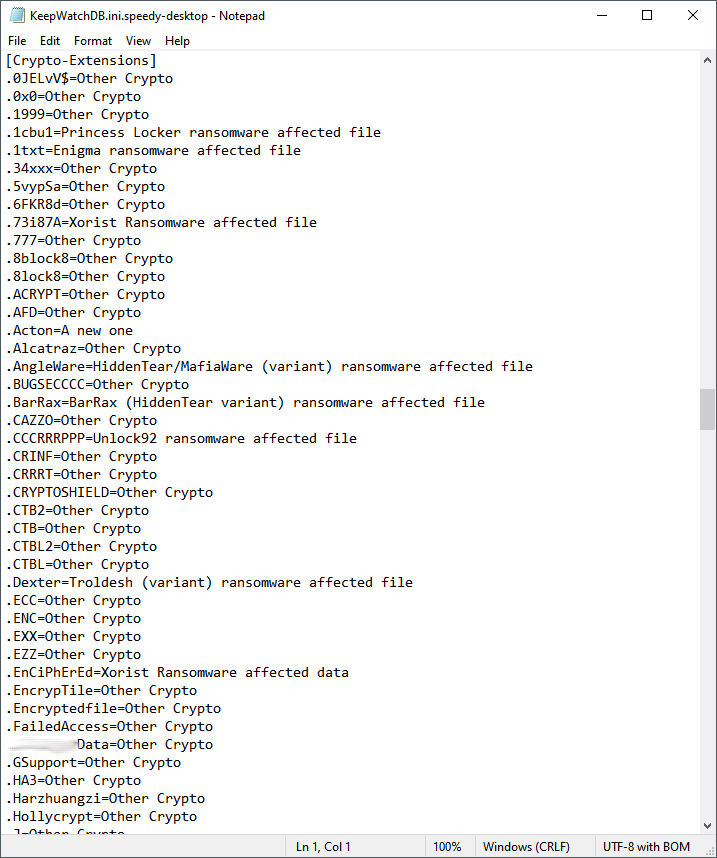
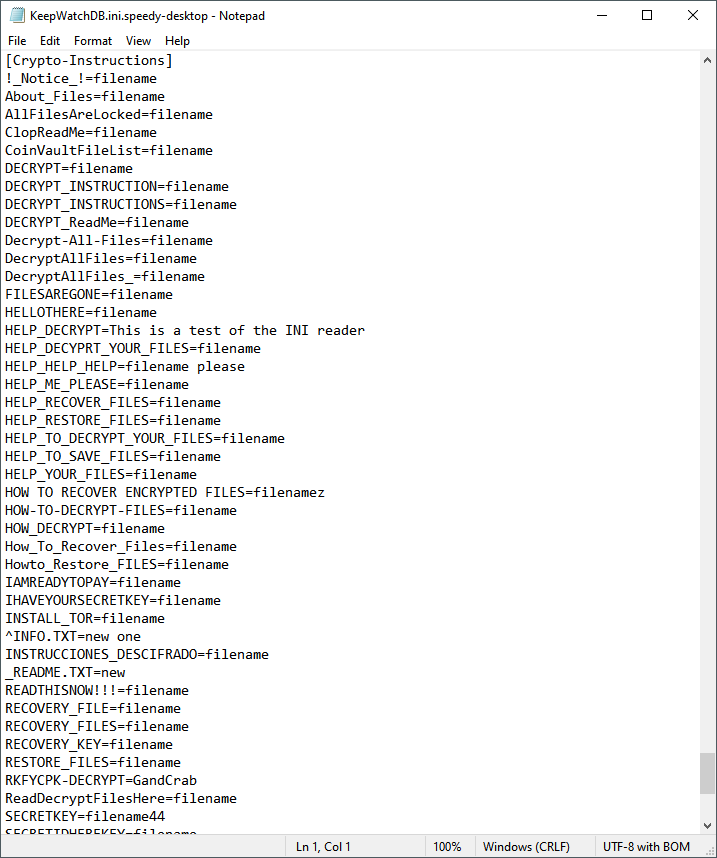
In order to detect malware, especially ransomware, the program has a database of file names and extensions that it regards as safe and others that are known to be dangerous. Users can update these files, but, I plan to have an autoupdate mechanism soon.
If the supplied SwithMail client has been configured, the program can also send email or text messages to one or more users.
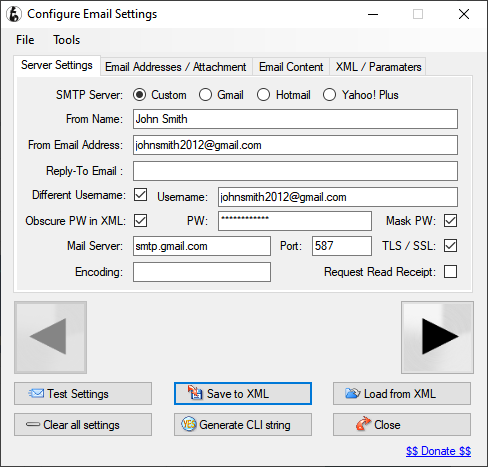
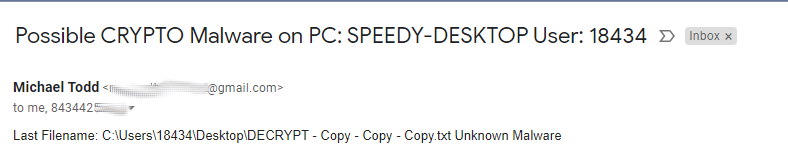 SwithMail settings are below, click on Configure Settings, fill in your email information and click Test.
SwithMail settings are below, click on Configure Settings, fill in your email information and click Test.
Click Save to XML and use the filename SwithMailSettings for IPs like 192.168.x.x or PCs not on a Domain). Change the filename to SwithMailSettingsWork for IPs like 10.x.x.x or PCs on a Domain).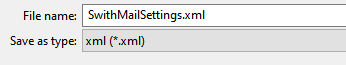
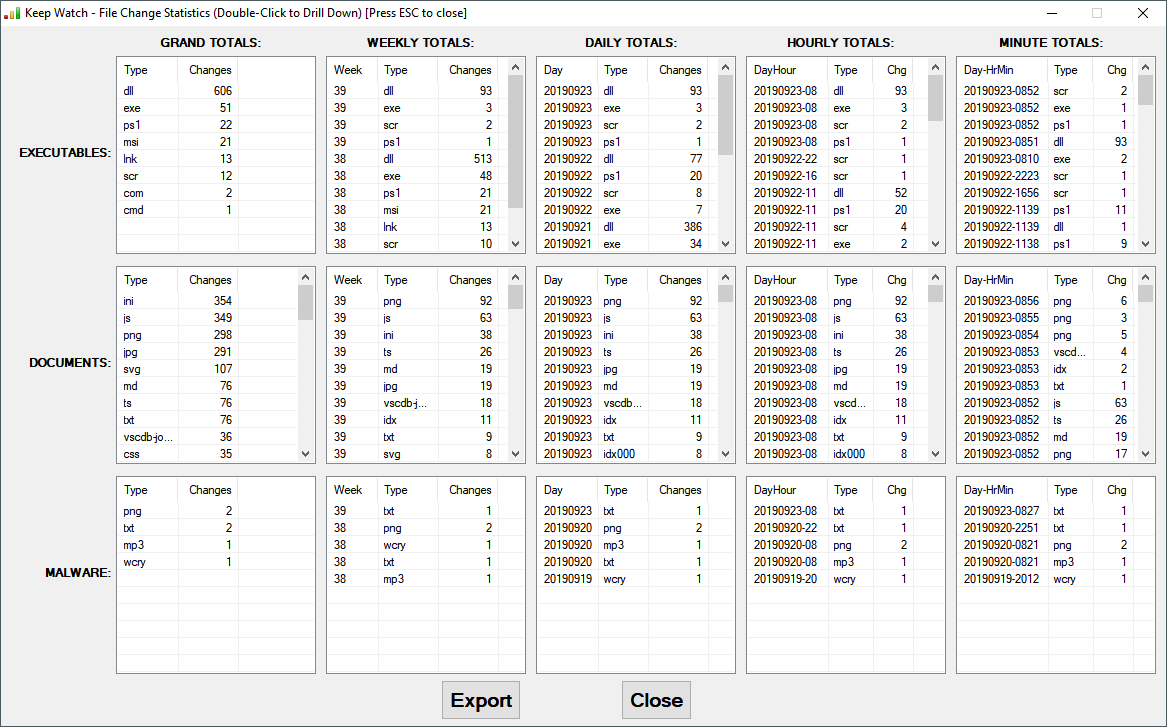
Keep Watch keeps up to 3 days of historical information on file changes. These can be viewed by selecting Show Change Stats from the menu or drop down list.
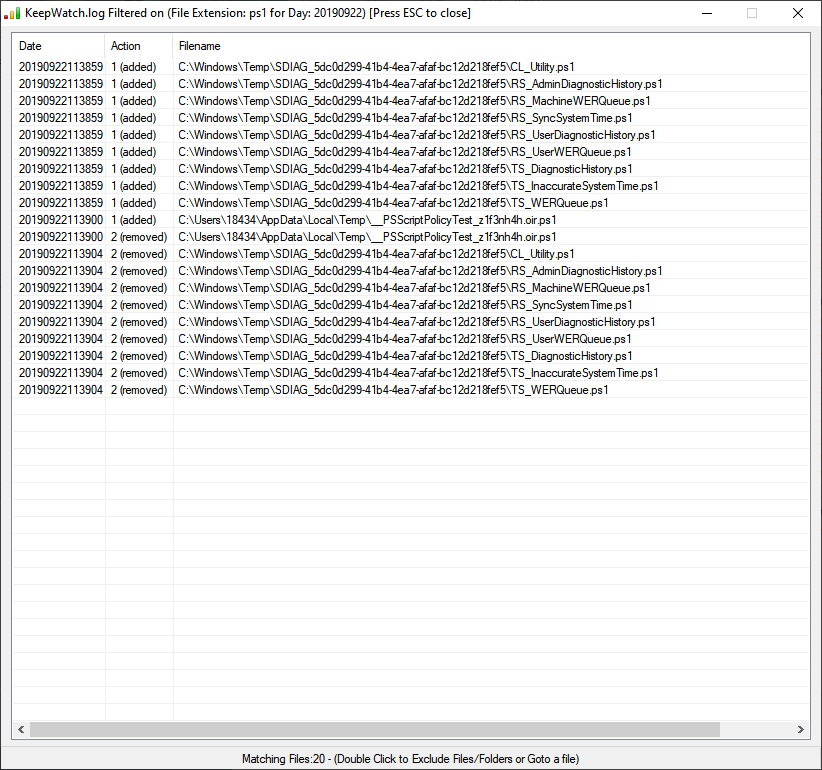
For example, I can see details on PowerShell script file changes from the Stats report by double-click on ps1.

 To summarize Keep Watch, if takes a snapshot of running processes, startup programs and existing file types and uses that information along with its malware database to alert users of what can be malicious activities.
To summarize Keep Watch, if takes a snapshot of running processes, startup programs and existing file types and uses that information along with its malware database to alert users of what can be malicious activities.
Users can get email alerts, they can also click Shutdown to turn off their computer and request IT support to help retrieve file which are still good. Users can Hide the program and Pause the program. If you are about to install a program or big upgrade then Pause the program or Exit it first. It’s best to Pause the program before Ejecting/Removing external storage devices also. The program will restart whenever a new drive/disk is detected.
![]()
Lastly, if you are going to be away from your computer for some time or over night, you can click on I am HERE and change your status to I am AWAY. When you are away, if the program detects too much file activity or malware/ransomware related filenames, it will send an email alert, display a 15 second warning then Shutdown the computer.